Today part of the April 2024 patch Tuesday, Microsoft released a bunch of security updates for its products and services, to resolve various vulnerabilities and bugs. April 2024 Patch Tuesday update, addressed 149 security vulnerabilities including three critical vulnerabilities and sixty-seven remote code execution bugs. It also addresses a series of other bugs related to performance and usability. These updates are important and install as soon as possible to protect your device from potential attacks and exploits. Let’s look at the highlights of the Microsoft Patch Tuesday update in April 2024 for Windows 11 and Windows 10.
What is Patch Tuesday Update?
Microsoft Patch Tuesday Update, the colloquial term for Microsoft’s Update Tuesday falls on the second Tuesday of every month, and brings security updates to fix vulnerabilities or recent bugs.
A vulnerability is a weakness or flaw in a software or hardware component that an attacker could exploit to gain unauthorized access, execute malicious code, or cause damage or disruption. A bug is an error or defect in a software or hardware component that could cause it to malfunction or behave unexpectedly. A security update is a software patch that fixes or mitigates one or more vulnerabilities or bugs.
A security update can have different ratings depending on the severity and impact of the vulnerability or bug it addresses. Microsoft uses four ratings: critical, important, moderate, and low.
- The critical update fixes a vulnerability that could allow an attacker to take complete control of a system without user interaction.
- An Important update fixes a vulnerability that could compromise data or functionality but require user interaction or specific conditions.
- Moderate update fixes a vulnerability that is unlikely to be exploited, but could still have some impact.
- A Low update fixes a vulnerability that is very unlikely to be exploited and has minimal impact.
Microsoft Patch Tuesday update April 2024
The April 2024 Patch Tuesday includes 149 security updates, of three vulnerabilities that were classified as critical, (As it allow privilege elevation, spoofing, or remote code execution) 145 are rated Important in severity. The critical updates affect Windows, Internet Explorer, Edge, Office, SharePoint, Exchange, and Azure DevOps Server.
As per the release notes, the April 2024 Microsoft Patch Tuesday Update fixed 31 Elevation of Privilege security issues, 67 Remote Code Execution bugs, 13 Information Disclosure vulnerabilities, 29 Security Feature Bypass Vulnerabilities, 7 Denial of Service Vulnerabilities, and 3 Spoofing Vulnerabilities.
Microsoft did not disclose any zero-days as part of today’s Patch Tuesday updates.
Microsoft’s April 2024 Patch Tuesday, which includes security updates for a total of 149 flaws.
Microsoft fixes three critical bugs in Windows Hyper-V
- CVE-2024-21322: Microsoft Defender for IoT Remote Code Execution Vulnerability
- CVE-2024-21323: Microsoft Defender for IoT Remote Code Execution Vulnerability
- CVE-2024-29053: Microsoft Defender for IoT Remote Code Execution Vulnerability
CVE-2024-21322: This vulnerability allows an attacker who has administrative access to the web application to execute code remotely on target systems. In simpler terms, if an attacker gains administrative privileges within the Defender for IoT web application, they can potentially take control of devices or systems connected to the IoT network.
CVE-2024-21323: This vulnerability involves a path traversal issue, where an attacker can manipulate file paths to access unauthorized files or directories. To exploit this vulnerability, the attacker needs to send a specially crafted tar file to the Defender for IoT sensor. Once the file is extracted, the attacker can send unsigned update packages and overwrite any file on the system. However, they first need to authenticate themselves and gain the necessary permissions to trigger the update process.
CVE-2024-29053: In this vulnerability, an attacker doesn’t need administrative privileges but must be authenticated to the system. This vulnerability also involves path traversal, allowing the attacker to upload malicious files to sensitive locations on the server. To exploit this vulnerability, the attacker needs access to the file upload feature and can then upload files to critical areas of the server, potentially leading to remote code execution.
Update for Windows client versions
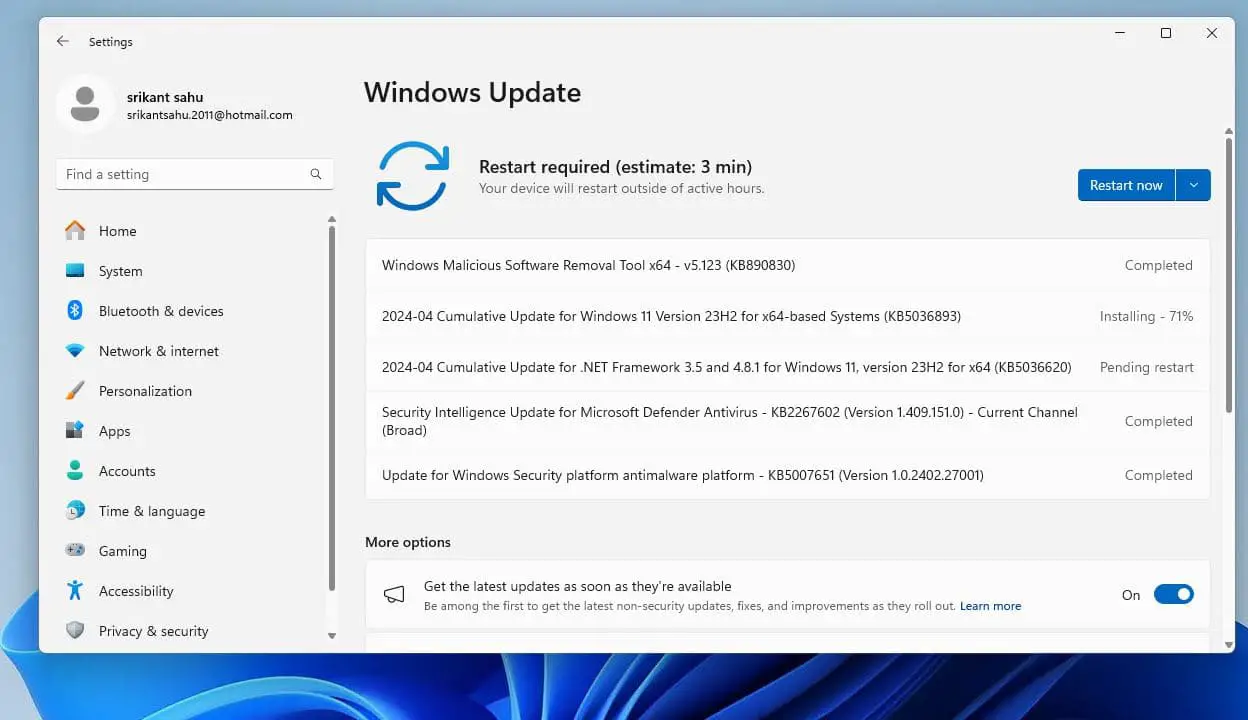
April 2024 (Patch Tuesday) Windows security updates are the following:
- KB5036893 (OS Build 22631.3447/22621.3447) for the latest Windows 11 version 23H2/22H2
- KB5036894 (OS Build 22000.2899) for the latest Windows 11 version 21H2
- KB5036892 (OS Builds 19045.4291) for the latest Windows 10 version 22H2/21H2
- KB5036896 (OS Build 17763.5696) for the latest Windows 10 version 1809
All these updates only include minor patches and security fixes, rather than any new features.
Note: Windows 11 was released with several new features and improvements as a free upgrade for eligible Windows 10 devices. Here is how to upgrade to Windows 11 for free.
Both Windows 11 KB5036893 and Windows 10 KB5036892 address security issues for your Windows operating system. Also, Windows 11 KB5035853 enables moment 5 features for all devices.
Download the Microsoft Security Update
To download and install the updates, users can use Windows Update, Microsoft Update Catalog, or other tools such as Windows Server Update Services (WSUS) or System Center Configuration Manager (SCCM). Users should also check for updates from other vendors that may be affected by the same vulnerabilities or use components from Microsoft.
Usually, security updates are automatically downloaded and installed via Windows update. Or you force Windows update from settings, Windows update, and check for updates to download and install the latest patch updates immediately.
Microsoft has published download links for Windows update offline installers if you prefer manual installation over Windows Update.
- Windows 11 KB5036893 (Version 23H2/22H2) offline installer Direct Download Link 64-bit.
- Windows 11 KB5036894 (Version 21H2) offline installer Direct Download Link 64-bit.
- Windows 10 KB5036892 (For versions 22H2 and 21H1) Direct Download Links: 64-bit and 32-bit (x86).
Windows 10 KB5036896 (for version 1809) Offline Download links
If you are Looking for Windows 10 version 22H2 ISO image, click here.
Or Check How to Upgrade to Windows 10 version 23H2 Using the media creation tool.
If you face any difficulty while installing these updates, Check the Windows 10 Update troubleshooting guide to fix the Windows 10 update KB5036892 stuck downloading, failed to install with different errors, etc.
FAQ on Patch Tuesday update
What is Patch Tuesday?
- Patch Tuesday is the colloquial term for Microsoft’s Update Tuesday which falls on the second Tuesday of every month.
When is Patch Tuesday?
- Patch Tuesday falls on the second Tuesday of each month. The upcoming Patch Tuesday is on 9 April 2024.
What is patching and why is it important?
- Patches are nothing but pieces of software code that are written to fix a bug in a software application that might lead to a vulnerability.
What kind of patch updates are released during Patch Tuesday?
- Predominantly security patch updates of varying severity like Critical, Important, Moderate and low are labeled and released.
What are CVE IDs?
- CVE ID – Common Vulnerabilities and Exposure ID is a format in which each vulnerability is disclosed and cataloged in the National Vulnerability Database (NVD).
Also Read
- Complete Review of Microsoft Windows 10 Operating system
- Solved: Microsoft Edge not working after the Windows 10 update
- can’t connect securely to this page ie11 or edge Windows 10
- Windows 10 Stuck Preparing Automatic Repair? Here is how to fix
- Everything About IP (Internet Protocol) Address – Purpose to Benefits explained