Today part of the April 2024 patch Tuesday update Microsoft has released Windows 10 KB5036892 and KB5036896 cumulative updates for versions 22H2 and 1809. The latest KB5036892 (build 19045.4291) for Windows 10 22H2 adds Spotlight wallpapers for the desktop. It also rolls out sports, traffic, and finance content on the lock screen. Additionally, it addresses several issues with touch keyboard, Windows Hello for Business, deadlock issue in CloudAP, Microsoft Edge fails to open on Surface Hub and more. Windows 10 KB5036892 is an important security update, and you should download and install the package as soon as possible. Microsoft has also published direct download links for Windows 10 KB5036892 offline installers to install it manually.
Windows 10 KB5036892 Release Summary:
- KB Article: KB5036892 for version 22H2, KB5036896 for version 1809
- OS Version: Windows 10 version 22H2 and version 1809
- Build: OS Build 19045.4291, OS Build 17763.5596 (For version 1809)
- Size: Download KB5036892 64 Bit, (832.1 MB), KB5036892 32-bit (460.1 MB)
- Release Date: 09 April 2024 Part of Microsoft patch Tuesday update.
- What’s new: Bing Spotlight integration on the desktop, you’ll get updates on sports, traffic, and money matters right on your lock screen. It also includes several bug fixes and improvements.
The full list of April 2024 Patch Tuesday updates for Windows 10:
- Windows 10 version 1507 — KB5036925 (OS Build 10240.20596)
- Windows 10 version 1607 — KB5036899 (OS Build 14393.6897)
- Windows 10 version 1703 — EOS
- Windows 10 version 1709 — EOS
- Windows 10 version 1803 — EOS
- Windows 10 version 1809 — KB5036896 (OS Build 17763.5696)
- Windows 10 version 1903 — EOS
- Windows 10 version 1909 — EOS
- Windows 10 version 2004/21H1/20H2/21H1 — EOS/EOS
- Windows 10 version 21H2, and 22H2 — KB5036892 (OS Builds 19044.4291 and 19045.4291)
Like previous Patch Tuesday releases, this Windows 10 update KB5036892 doesn’t come with any new features. Rather, the focus is on security, reliability improvements, and fixes across the board.
Note: Windows 11 was released as a free upgrade for eligible devices, check if your PC is eligible for the Windows 11 free upgrade
Windows 10 KB5036892 Download
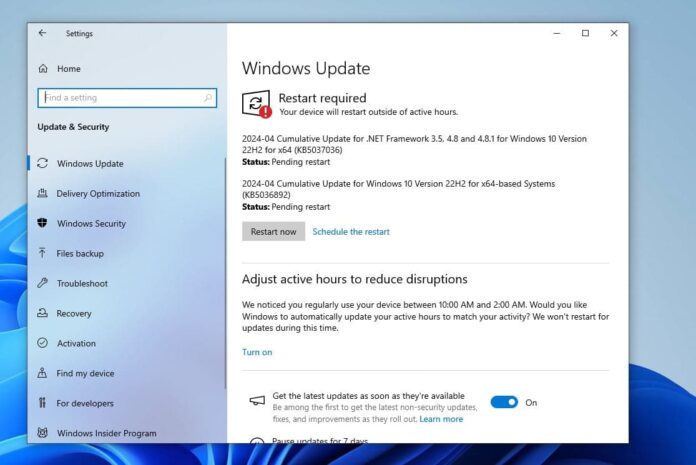
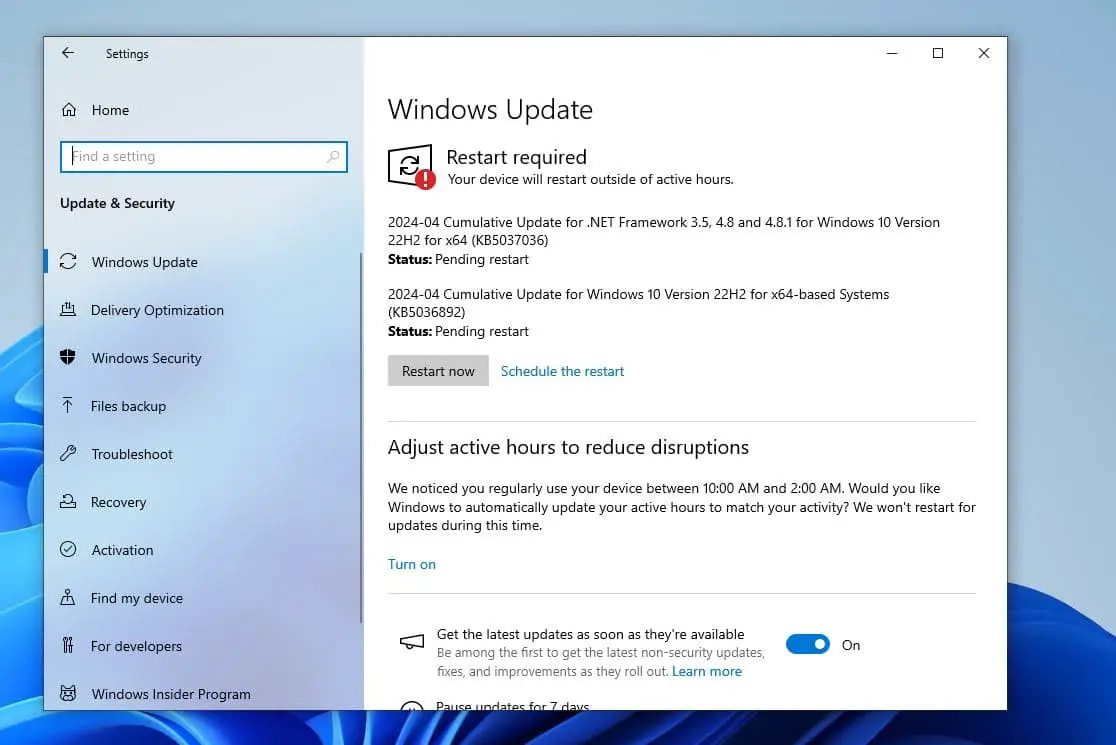
Since Microsoft patch updates are mandatory updates, Windows 10 KB5036892 downloads and installs automatically. Once installed, you will need to restart the system for the changes to take effect.
To Download Windows 10 KB5036892 using Windows Update, follow the steps below:
- Open Settings using Windows key + I. Click Update & Security then Windows Update.
- In the right-hand pane, click on the Check for updates button. You will see the following patch, it automatically downloads and installs on your device.
2024-04 Cumulative Update for Windows 10 Version 22H2 for x86-based Systems (KB5036892)
Ensure your device is connected to stable internet to download update files from the Microsoft server. Once done you need to reboot your computer to apply changes.
- If you are looking for the latest Windows 10 version 22H2 ISO, click here.
- In addition, you can download the latest Windows 11 ISO images here.
Download Links for Windows 10 KB5036892
As usual, the patch can be installed from the Update Catalog as well here Windows 10 KB5036892 download Offline installer direct download links 64-bit and 32-bit (x86).
- locate the patch next to the correct edition and version of the operating system.
- To install the update, simply run the downloaded MSU file and Windows will automatically install the cumulative update.
So what exactly is Windows 10 KB5036892?
Today’s update is all about security fixes and improvements. On the release note, Microsoft noted, that Windows 10 KB5036892 makes miscellaneous security improvements to internal OS functionality.
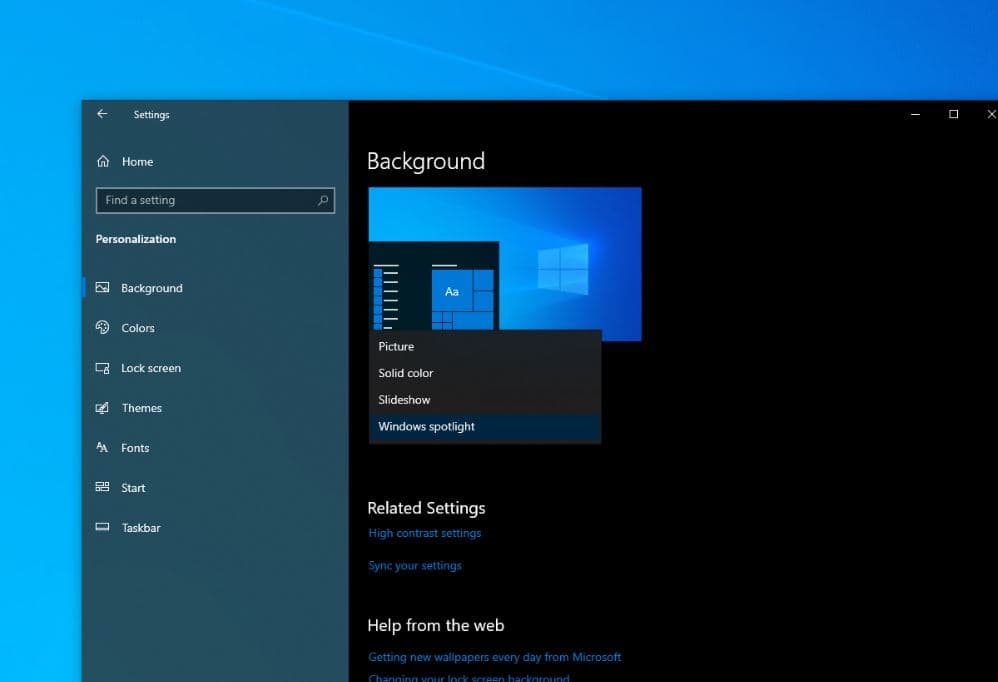
In addition, Microsoft noted users can now add Windows Spotlight to their desktop background, which downloads and rotates images for your wallpaper. To configure this navigate, to Settings > Personalization > Background > Personalize your background and choose Windows Spotlight.
Also, Microsoft is rolling out more information including weather, sports, traffic, and finance content on the lock screen. This can be enabled or disabled from Settings > Personalization > Lockscreen.
After installing today’s update, you may get invited to upgrade Windows 11, if your device is eligible. This update adds search highlights to the taskbar search box for the European Economic Area. Well above features might not be available to all users because it will roll out gradually.
This update also resolves an issue with the touch keyboard failing to open and enhances Windows Hello for Business by allowing IT admins to disable post-logon provisioning via MDM.
It addresses problems affecting the COM+ component leading to application unresponsiveness, ensures app and feature availability post-Windows 11 upgrade, and fixes a deadlock in CloudAP.
The update also resolves access issues to network resources from Remote Desktop sessions with Remote Credential Guard enabled, fixes a launching issue for Microsoft Edge on Surface Hub, and strengthens security through updates to the Antimalware Scan Interface (AMSI).
Additionally, it corrects a mismatch in time service configuration between the Windows Settings app and MDM or GPO settings, fixes image loading issues with LoadImage(), and addresses scanner connectivity problems.
The update also updates COSA profiles for mobile operators, ensures proper AppLocker rule enforcement, fixes Group Policy service failures post-audit policy application, and enhances the reliability of Virtual Remote App products.
Windows 10 KB5036892 known issues
However, it’s essential to note a couple of known issues. Windows devices with more than one monitor may experience desktop icon movement issues or alignment problems when using Copilot in Windows (in preview).
Copilot in Windows (in preview) is currently not supported when the taskbar is located vertically on the right or left side of the screen. Users may encounter compatibility issues in this configuration.
We recommend reading the complete changelog Microsoft support site here.
Uninstall Windows 10 KB5036892
If installing KB5036892 causes issues on your device you can uninstall the update to revert the changes.
Uninstall KB5036892 using the Windows Update History tool
- Go to Windows Settings (Windows key + I) –> Update & Security –> Windows Update.
- From the right-hand pane, click on View Update History.
- Now click on Uninstall updates.
- Select Update for Microsoft Windows (KB5036892) and press the Uninstall button.
Uninstall KB5036892 using command-line
Another quick way to uninstall this update is by using the command prompt. Here are the commands:
- Open Command Prompt (Run –> cmd)
- Run the following command:
wmic qfe list brief /format:table - This will show all the updates installed on the computer. Make sure KB5036892 is on the list.
- To uninstall the update, run the following command
wusa /uninstall /kb:5035853
The system needs to be restarted after uninstalling the update.
In addition, Microsoft has noted Windows 10 version 21H2 reach end of service on June 11, 2024. That means devices no longer receive monthly security and quality updates that contain protection from the latest security threats. Microsoft recommends Install the latest version 22H2 or upgrade to Windows 11
Windows 10 KB5036896 what’s new?
KB5036896 (OS Build 17763.5696) for Windows 10 version 1809 also brings a few bug fixes and improvements.
This update resolves a problem where the touch keyboard fails to open intermittently, improving accessibility for users. It fixes a connectivity issue that prevents access to network resources from a Remote Desktop session when Remote Credential Guard is enabled on Windows 11, version 22H2 or higher.
The update also addresses a critical problem with DNS servers encountering Event 4016 due to an LDAP timeout during DNS registrations, leading to failed name registrations with AD DS until the DNS service is restarted.
Furthermore, it fixes an issue causing devices to shut down 60 seconds after authentication with a smart card on a remote system. Lastly, it addresses a discrepancy in LDAP where users with expired temporary group memberships still appear in search results, even after being removed by Active Directory.
If you experience problem installing Windows 10 updates or the update stuck download here are a few solutions.
Also read:
- Difference Between Windows 10 Feature Update and Cumulative Updates
- Windows Update won’t download or failed to install on Windows 10 (Solved)
- How to Share Files and Printers Between Two Windows 10 Computers
- Windows 10 keeps shutting down and restarting automatically. Try these solutions
- Complete Review of Microsoft Windows 10 Operating system