A firewall is a network security tool that monitors and controls the incoming and outgoing traffic in a computer network. It can be either hardware or software-based, and it works by applying a set of rules to the data packets that pass through it. Depending on the rules, the firewall can accept, reject or drop the traffic. Overall Firewalls are essential for protecting any network from malicious attacks and unauthorized access. In this article, we will explore what a firewall is, how it works, and what are some of the benefits of using a firewall in a computer network.
What is a firewall?
The term firewall comes from the concept of physical walls that are used to slow down the spread of fire until it can be extinguished. Similarly, a network firewall is a barrier that slows down or stops the spread of web threats by managing the web traffic in a network. A firewall establishes a boundary between a trusted network and an untrusted network, such as the Internet. A firewall can also create subnetworks or zones within a network to isolate different types of devices or services.
Types of Firewalls:
A firewall can be implemented as a hardware device, a software program, or a combination of both.
- A hardware firewall is a dedicated device that is connected to the network and acts as a gateway for all the traffic that enters or leaves the network. These Firewalls are generally expensive and are designed majorly for advanced users.
- A software firewall is a program that runs on a computer or another device and filters the traffic that passes through it. For example, the Windows Defender firewall protects computers connected to the Internet and LAN against malicious attempts of hackers hunting your privacy and security.
- A hardware firewall can provide protection for multiple devices in a network, while a software firewall can provide protection for individual devices.
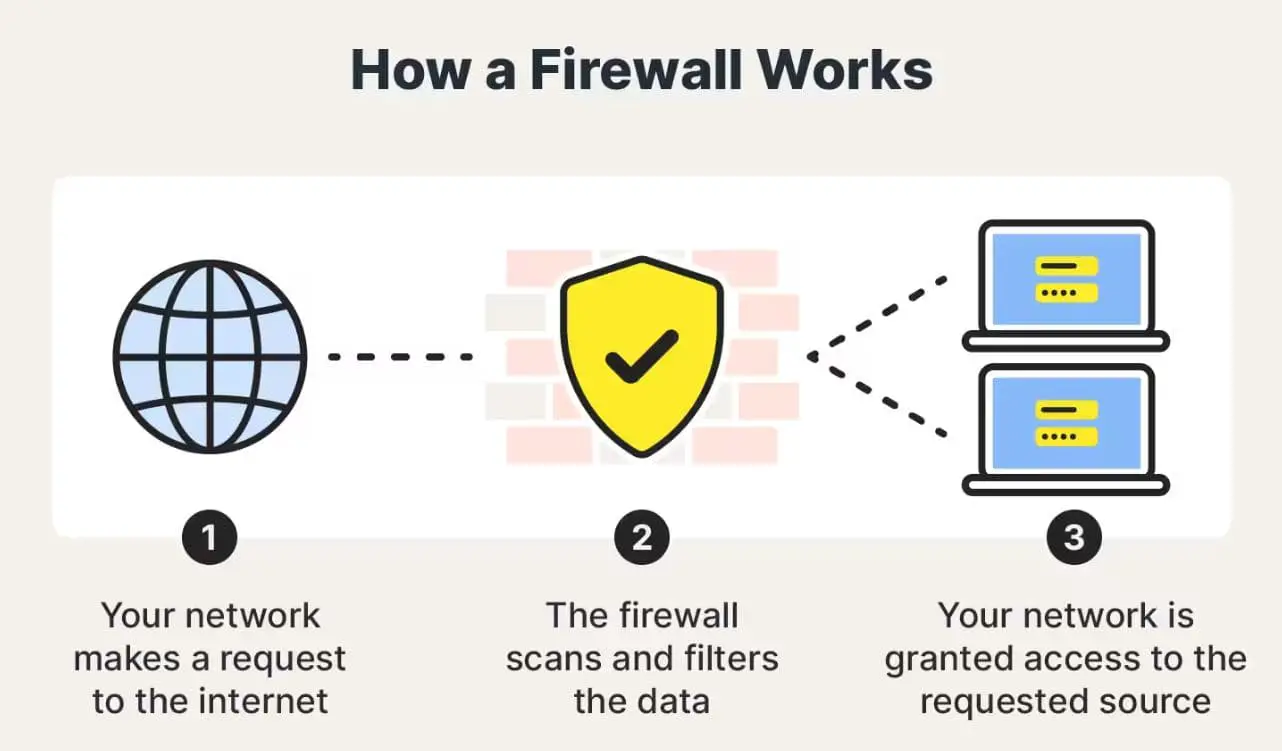
How does a firewall work?
A firewall works by inspecting the data packets that travel between networks or devices. A data packet is a unit of information that contains the source address, the destination address, and the payload or content of the message. A firewall matches each data packet against a set of rules that are defined by the network administrator or the firewall vendor.
The rules specify what kind of traffic is allowed or denied based on various criteria, such as:
- The source address: The IP address or domain name of the sender of the packet.
- The destination address: The IP address or domain name of the receiver of the packet.
- The protocol: The type of communication method used by the packet, such as TCP, UDP, or ICMP.
- The port number: The number that identifies the specific service or application that the packet is intended for, such as HTTP (80), FTP (21), or SSH (22).
- The content: The actual data or information that the packet carries, such as keywords, signatures, or patterns.
Based on these criteria, a firewall can perform one of these actions on each data packet:
- Accept: Allow the packet to pass through the firewall and reach its destination.
- Reject: Block the packet from passing through the firewall and send back an error message to the sender.
- Drop: Block the packet from passing through the firewall and discard it without sending any response to the sender.
A firewall can also perform other functions, such as:
- Encrypting or decrypting the data packets to ensure secure communication between networks or devices.
- Logging or auditing the data packets to record and analyze the network activity and security incidents.
- Alerting or notifying the network administrator or other stakeholders about any suspicious or malicious traffic.
Advantages of using a firewall in a computer network
Using a firewall in a computer network can provide several benefits, such as: Prevent unauthorized access, Monitors network activity, Filter unwanted content, encrypts your data and prevents it from being intercepted or stolen by cybercriminals and more.

Firewall is the first name when you want to defend your computer and information against hackers. Without Firewall protection, hackers can take control of your computer. Not only can they install malware on your system but also steal your personal and financial data. However, with a correct firewall configuration, you can get remote access disabled.
Online gaming poses great security risks because most malware is designed to target gamers playing on unsecured servers. In this case, firewall security remains the best option to shield your privacy from all potential attempts.
Using your firewall, you can block any irrelevant website that you don’t want some specific user/s to visit. This kind of security is mainly needed in corporate domains and homes where there’s an undeniable need for keeping some specific content out of reach from users.
A firewall can encrypt your data and prevent it from being intercepted or stolen by cybercriminals. A firewall can also prevent data leakage by blocking unauthorized outbound traffic from your network. This can help you comply with data privacy regulations and protect your intellectual property.
You can configure your firewall program to limit the network bandwidth allowed for non-essential videos, images, and music, hence keeping the bandwidth for important traffic.
It can Enhance the performance and efficiency of the network by filtering out unnecessary or unwanted traffic. A firewall can reduce network congestion and bandwidth consumption by blocking or limiting the traffic that is not relevant or important for the network operations or objectives.
Allow network administrators to customize the security policies and rules according to the needs and preferences of the organization. A firewall can provide flexibility and granularity in defining and enforcing the network security rules based on various factors, such as the type, source, destination, content, or time of the traffic.
Providing audit logs and reports that help in monitoring and analyzing the network activity and security incidents. A firewall can record and store the details of the data packets that pass through it, such as their source, destination, protocol, port, content, action, date, and time. These logs can be used for troubleshooting, auditing, compliance, forensics, or reporting purposes.
Facilitating compliance with various regulations and standards that require network security. A firewall can help an organization to meet its legal or contractual obligations regarding the protection of its network and data from unauthorized access, disclosure, modification, or destruction.
Also read:
- What Is The Difference Between A VPN And A Proxy and how they work?
- How to disable the Windows SmartScreen filter in Windows 10
- The File Is Too Large for the Destination File System (Solved)
- This request was blocked by the security rules error code 15 or 16
- Remote Desktop Black Screen Problem Windows 11 (solved)
Sources:
– Introduction of Firewall in Computer Network – GeeksforGeeks
– What is a Firewall? How Firewalls Work & Types of Firewalls – Kaspersky
– Firewall (computing) – Wikipedia